Each year the challenges facing cybersecurity practitioners change, a result of many factors. Among them are: the increasing sophistication of attacks employed by threat actors, the ever-changing design of IT infrastructure (i.e. cloud migration), and external influences such as the pandemic.
While companies have been investing more in cybersecurity to keep their environments safe, challenges remain. One issue is simply the volume: organizations must respond to the latest threats while simultaneously building basic defenses against the old classics.
Here are what we consider to be the five biggest cybersecurity challenges ahead of us as an industry.
1 Vulnerability Management Failed Us
The vulnerability management industry failed us and requires a new approach for organizations to maintain good cyber hygiene.
Keeping up with the rate of discovery of new vulnerabilities is a losing battle. On average, it takes 60-150 days to patch a vulnerability in an enterprise-sized organization, and the shear volume of newly introduced and newly discovered vulnerabilities is overwhelming. The legacy method of using a scanner that reports all the vulnerabilities then assigns those to a different department (IT) to remediate hasn’t worked.
Earlier in 2021, we addressed the issue of the failed vulnerability management paradigm in our article Why the Vulnerability Management Industry Failed Us, and What To Do About It.
It is noteworthy that Qualys, founded in 1999 on its vulnerability scanning solutions, added patching to their solution in 2019. Their VMDR vulnerability management tooling, which uses a singular cloud agent on the endpoint, and combines multiple critical features that address asset management, realtime vulnerability and misconfiguration detection, and automated patching.
2 Vendor/Third Party Risk Remains a Wide-Open Threat Vector
Businesses rely on their third-party software and SaaS vendors. If one of those vendors is breached and their software is used in your company or they provide a SaaS service that contains your data, you’ve likely been breached as well. There is nothing you can do about it today, and that assumes affected parties are even aware they’ve been breached.
“Supply chain attacks” became mainstream this year by demonstrating how an attacker could attack a vendor, hide in their products, and attack all their customers when that software is distributed.
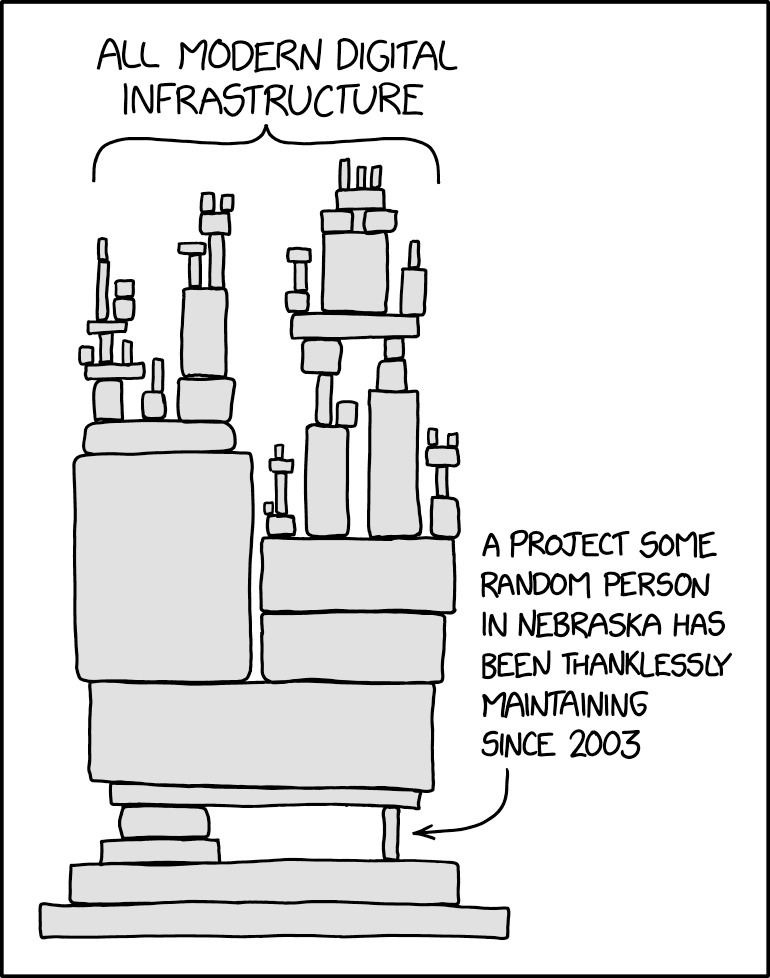
This concept hit the mainstream in December 2021 as the legacy Java logging library Log4j, used in literally thousands of products from obscure open source projects to high profile enterprise software was found to have a critical remote code execution vulnerability. Administrators and security professionals spent the final weeks of the year in mad dash to identify which software in production contained the vulnerability in order to apply patches. It was yet another wakeup call for the industry that sometimes giants stand on the shoulders of the smallest open source projects but the visibility for their use is underdeveloped.
And prior to that, the SolarWinds attack from spring 2021 revealed how exposed and vulnerable customers are to the risk that any vendor could be compromised at any time, and distribute compromised malicious code via legitimate update channels.
Today, VRM Vendor Risk Management is the only available mitigation strategy. In its current form it amounts to surveying the vendor to ask them questions about cybersecurity and contractual agreements as a means to mitigate risk.
The legacy paradigm of third-party risk management is failing to keep up. Periodic assessments and audits that use standardized and generic evaluation criteria are not catching risks. Combine this with the challenge of rapid onboarding of new service providers—organizations are simply unable to research associated risks quickly and effectively.
This signals a shift in how it should be done. Third-Party Risk Management and Vendor Risk Management must evolve to utilize technology that provides visibility through a software Bill of Materials (BOM).
Software vendors must adopt the paradigm of Shift Left Security where security is part of the fabric of the software design process so that BOMs are easy to provide to customers, and vulnerabilities can be readily reported.
3 Endpoint Protection Is Failing
The commonly accepted statistic is that roughly 90% of vulnerabilities affect the endpoint. The stat holds up when some of the more significant and recent high profile cybersecurity attacks have targeted business endpoints.
While the trend away from traditional anti-virus and anti-malware solutions continues with the shift to Endpoint Detection and Response products, new research shows those aren’t doing as great a job as everyone thought, either:
Identifying weaknesses in endpoint protection is essential to avoid becoming the next target. At this point the solution seems to be layering coverage: combining traditional endpoint protection with newer EDR products, then adding some type of SOC or monitoring services to make use of all available telemetry.
And finally, the weakest part of the endpoint is the human sitting at the keyboard with mouse in hand; recurrent phishing awareness training goes a long way toward eliminating what we know comprises the majority of initial attack vectors.
4 Data Security Remains a Huge Challenge
There has been a surge of data breaches affecting high numbers of organizations and millions of users.
High profile breaches occur several times a year, the most recent being GoDaddy who had their managed WordPress platform compromised, resulting in a reported 1.2 million active and inactive customers’ email addresses and customer numbers being exposed.
Wireless carrier T-Mobile even had two breaches in 2021.
Why do data breaches continue to occur at such a high level among Fortune 500 companies who presumably have the best security that money can buy? It’s not complicated—security is a game of predictions and due diligence in locking down what can be locked down.
In the case of GoDaddy, some WordPress admin passwords were compromised. At that point access is trivial and the scale of the data breach comes down to how much time bad actors have to transfer files and data before—or if—they’re detected. The same old vulnerabilities, misconfigurations, and shortcomings in security protocols contribute to the outcome.
Data security is as much an institutional challenge as it is a technological hurdle. It’s a complex intersection of specialized tools, integration with multiple systems, and training employees to understand the core issue and practice responsible data handling. The products exist and the best practices are published—organizations just have to commit.
One bright spot for the industry are emerging next generation data security companies such a BigID and Open Raven, who are attacking the problem with cloud-first, high-visibility approaches.
5 Small Businesses Are Being Left Behind
Cybersecurity innovation happens in the large enterprise. Whether it’s the startups or the large software vendors, all of their newest cybersecurity technology targets the largest companies who can pay the most for their products.
But 99.9% of businesses in the US qualify as small, and can’t afford a combination of tools from each of cybersecurity defense categories that are as good as the enterprise versions, nor can they afford the trained resources to use the tooling.
Effectively, small businesses are being hung out to dry. They’re prime targets for malware, ransomware, data breaches, and other external threats and lack the tooling, training, and resources to prevent and respond to security events.
For the first time in cybersecurity history funding and resources are starting to pour into this problem. Most notably groups like Arctic Wolf and novaSOC are attacking the problem.




