You may have been brought up with computer technology, but the digital age crept up on your parents, who’ve adapted to it as best they can. Remember, using a rotary-dial phone probably seems not that long ago for them, and is likely a much fonder memory than say…recalling their usernames and passwords. But in present-day life, which depends so heavily on Internet usage, older adults are disproportionately at risk of becoming victims of cybercrime.
Maybe they’ve heard about some of the more prominent cyberattacks in the news, but likely think cybercriminals won’t see them as targets. Think again, Mom and Dad. Cyberattackers disproportionately target people over the age of 60. There’s no better combo for a mark than an older person with substantial retirement savings and poor familiarity with technology or cybersecurity precautions. In fact, according to many reports, the amount cybercriminals steal from our aging population annually exceeds $100M and increases every year.
In light of the upcoming Father’s Day, we’d like to urge our readers to teach their parents about cybersecurity. In 2022, awareness of cyber threats is mandatory for Internet users of all ages to protect data, finances, and identity, but those users over 60 are particularly vulnerable because they sometimes struggle with technology. Here’s a rundown on what they should know:
What’s in a Password?
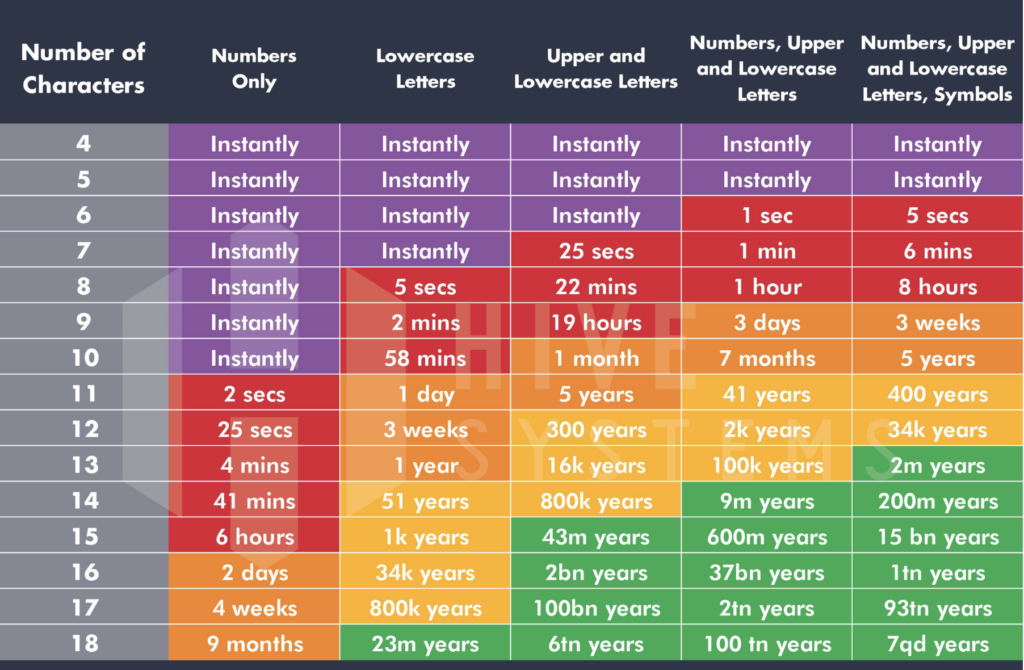
Having secure passwords is essential for everyone. Passwords under six digits can be cracked in seconds using brute force (automated trial and error.) This chart emphasizes how quickly it can happen based on length and complexity. Those easy-to-remember passwords parents love that consist of children or pet names? Trivial to crack.
A typical objection from parents will be that they can’t remember all their passwords. Luckily, they don’t have to anymore. Users of any age are advised to use a password manager such as 1Password, Bitwarden, or LastPass. It requires only remembering a single master password to access a vault of complex and unique auto-generated passwords for every account, across all your computers and mobile devices. Password managers can even store secure notes, only readable with the master password.
While getting parents on track with better password practices is a good first step, there are still more important lessons to learn.
Multifactor Authentication (MFA)
The older generation often operates out of a single email account for all their services: bank accounts, social media platforms, e-commerce, etc., making that one account the key the kingdom. So it should be explained to parents that Multifactor Authentication, or MFA, is simple and easy way to require both something you know and something you have in order to gain access.
A user inputs their username and password, but then must complete a third step in order to login. This comes in the form of a mobile device using SMS or an authenticator app like Authy, Google Authenticator, or Symantec VIP to generate a unique and short-lived code to enter.
Most websites for major services in banking, finance, healthcare, insurance, and even social media now have an option to use multifactor authentication. Banks usually require it, but email providers and social media platforms such as Facebook and Instagram have MFA available as an option.
This adds a level of protection that will deter most cybercriminals from getting into accounts to steal the personal information that allows them to impersonate or extort money from unsuspecting or uninformed older users. Access to an email account also gives hackers additional tools in the form of contacts, which they can use to construct even more contrived attack narratives with trusted individuals.
Once you explain how MFA works and assist them in setting it up, your parents will be better protected when accessing their accounts, even if a password is compromised.
As long as they don’t lose their phone.
Phishing and Email Security
The most pervasive strategy among cybercriminals is to attack via email. It’s often used to gain access to systems and spread malware. Not only in business environments, but also in personal computers and home networks. Crooks can cast a wide net with little effort to catch a gullible user.
A method that hackers have leveraged successfully is phishing. According to the 2021 IC3 Elder Fraud Report, there were 5,831 cases of phishing against the Over 60 age group last year. This threat is very real since aging parents are very susceptible to the tricks used in phishing campaigns.
There are two main ways to be compromised via phishing:
- Click a link in the email that launches some form of malicious attack (malware delivery, virus, ransomware), or…
- Being persuaded to provide sensitive information that could lead to accounts being compromised.
Typical scams that target the elderly include:
- Asking for help: In this campaign, the cybercriminal portrays an immediate need for financial assistance usually pretending to be a friend or relative such as a grandchild.
- Prize winner: A text message or email is arrives, stating they’ve won a big prize and requests their personal details to claim it.
- Bank account compromised: An urgent email arrives that appears to be from their bank, alerting them of suspicious activity. It asks that they click a link where they will confirm account details. The link actually leads to a fake site where bad guys collect the sensitive information the user submits.
- IRS notices: Notices from the IRS are alarming and trigger an emotional fear response. It is one of the reasons cybercriminals use this persona. These emails often threaten penalties for not paying up or providing the demanded information.
Tips for safer emailing
- Don’t act on the contents of emails: Because phishing depends on gullible users acting on the email’s coercive message by clicking or contacting the email/phone number in the email, a good approach is to just cut out the middleman. Go to the source. If it’s banking related, open a browser manually, type in the bank’s URL or use a bookmarked link. Then login. The bank’s internal messaging will alert you to any legitimate problems. Or simply call the bank directly using the phone number posted on their website or the back of your bank card.
- Don’t respond to emails requesting information: Legitimate businesses and internet-based services will never ask for passwords or identifying information. Ever. The only exception to this is if you call their support phone number, they will request details to prove that you, the caller, are who you say you are.
- Be vigilant with ALL emails: Teach parents to mistrust emails demanding some kind of action, how to spot the dead giveaways for fake or scam emails, such as misspellings, overly cordial greetings, poor English, and links to strange domains. Teach them to hover or tap/hold to see a link before it’s clicked.
Fake E-Commerce Websites
A newer scam relies on the normalization of e-commerce in society: fake websites that charge your credit card and don’t deliver.
For users of any age, using Google to search out the best price on an item you’re looking to buy is a normal. Google Shopping lists results for all the retailers who carry the item being searched, and can rank them by price or relevance. Unfortunately, the latest scam is to prop up a website using some catchy but meaningless Web 2.0 name, like something that would be made fun of in HBO’s Silicon Valley. The site will have the exact item you searched, for sale, in stock, free shipping, and for a price that is just too good to be true—high enough to be realistic, but low enough to make suspending vigilance worth the risk. And they have great SEO—Google picks these up right alongside the legitimate ones.
The site is real enough to take your payment card details and charge it. But they do not fulfill the order. Maybe they’re caught and shut down by the hosts after a short while, but a new one will pop up again to take its place.
Tell-tale signs of fake e-commerce sites are: recently registered domain names, use of legitimate e-comm platforms like Shopify, and difficult-to-find owner contact information. They somehow launder the money from charging credit cards quickly enough to avoid chargeback from your bank.
For this reason, parents should be advised to check sites like Trustpilot.com to vet lesser-known e-commerce sites. And they should always use a credit card with fraud protection, never a debit card even though it may use the VISA or Mastercard authentication network. Money debited from a checking account is often impossible to recover, while credit card banks will just wipe the charges away and refund the money.
Other Scams
Attacks against the aging population sadly aren’t limited to hacked systems and phishing scams. According to the IC3 report, the top cybercrime against the elderly is the tech support scam, which had 13,900 victims in 2021.
A laptop or desktop is coincidentally having some issues when a popup advertisement appears for over-the-phone tech support. Thinking it’s a genuine offer, they call the phone number listed and speak to an unknown tech support agent who assists them in installing antivirus or other software. Now the system is inoperable and the so-called tech support agent is unreachable. Who was this tech support person?
It’s just one method cyber criminals leverage to steal bank accounts, passwords, identities, and other personal information from users who sadly don’t have a sense for what’s legitimate and what’s a scam. Your family members can be shown how to avoid these types of incidents. Share these tips with them to get the ball rolling:
- Never share personal information with someone you don’t know or haven’t met face-to-face.
- Without video chatting on Zoom, Messenger, Facetime, or meeting someone in person, don’t trust who they purport to be.
- Be cautious when you receive a message on Facebook from someone claiming to be an old friend, especially if the message contains a link to click on in it.
- If a person claims to be overseas for a job it is a red flag. Many scammers say this to avoid connecting on a video chat or to avoid meeting in person.
- If something asks for immediate action, requires personal information, or sounds too good to be true be wary and watch for suspicious activity.
- Make it difficult for hackers to crack your passwords by using a password manager.
- Use anti-malware/anti-virus solutions and firewalls to block threats.
- You will never receive calls from government entities telling you that you owe money or attempting to collect payment.
If you suspect identity theft has occurred, get in touch with government authorities on this site.
Explaining Cybersecurity
While a cybersecurity event can be a frightening for anyone, understanding how they can happen and how to avoid one can make all the difference.
Give some peace of mind to Mom and Dad and your family by explaining to them what they should know about cybersecurity and the risks that await on the Internet, and sleep a little better yourself.